The Ultimate Guide to Encryption
A curated Indian edition of TechDay news, analysis, interviews, reviews, job moves, and related resources for Encryption.
What to know about Encryption
Encryption plays a crucial role in protecting digital information from unauthorized access, ensuring privacy and data security in an increasingly connected world. This tag gathers diverse stories on encryption technologies, strategies, and challenges faced by enterprises and individuals alike.
Recent discussions highlight the rising adoption of quantum-safe encryption, cloud-based key management solutions, and zero trust architectures, reflecting the evolving cybersecurity landscape. Companies such as DigiCert, Entrust, Gemalto, and others are actively advancing encryption offerings to prepare for emerging threats like quantum computing and sophisticated malware leveraging encrypted channels.
Readers exploring this tag can learn about innovations in encryption software and hardware, the importance of encryption in data protection regulations, and the complexities of managing encrypted traffic to prevent security blind spots. The collection also emphasizes the critical balance between privacy, regulatory compliance, and safeguarding against malicious actors who exploit encryption.
Whether you are a cybersecurity professional, IT decision-maker, or simply interested in data protection, following these stories will deepen your understanding of encryption’s essential role in securing information today and in the future.
Indian Encryption News
Regional stories with direct local relevance
QNu Labs quantum security passes fibre network test
The study suggests quantum-safe encryption could be deployed on existing telecom fibre without disrupting 10 Gbps data traffic.
Ramco unveils Chia, an AI agent for service workflows
Ramco launches Chia, a no-code conversational AI agent to orchestrate complex, multi-step service workflows across enterprise systems.

Makop ransomware group sharpens tools in India focus
Makop ransomware pivots to India with RDP brute force, privilege exploits and GuLoader as it leans on basic flaws over bespoke tools.

AONMeetings to launch low-cost video calls in India
AONMeetings to launch browser-based video calls in India within two weeks, with local plans from INR ₹169 a month including webinars.
India drops mandatory Sanchar Saathi app on smartphones
India scraps mandatory Sanchar Saathi app on new phones, easing privacy fears over deep-access government software on Apple and Samsung devices.

Edelweiss AMC cuts costs & boosts agility with Snowflake AI Data Cloud
Edelweiss AMC boosts agility and cuts data costs by 50% after upgrading to Snowflake AI Data Cloud, enabling faster reporting and personalised investor services.
Analyst Insights
Research and market analysis connected to Encryption
Protegrity launches AI Team Edition for secure inferencing

Survey finds organisations struggle to secure unstructured data

DigiCert posts record Q4 ARR after expansion spree

Xiid & Cytex link AI governance with zero trust access

Gigamon named 2026 public sector observability leader
Expert Columns

Proof beats promise: The trust crisis AI is creating

The why and what of FIPS 140-3 validation in modern cybersecurity

Why AI-powered security needs network telemetry across the hybrid cloud

Atlassian scales AI search with OpenSearch on Kubernetes

Hexnode CEO on how fintech breaches multiply where device visibility ends

Generative AI fuels alarming surge in intimate image abuse

2026 begins: Crypto's heavyweight rumble - round by round

Securing the future: Simplified management, Scalable growth, and built-in compliance for K-12

Enterprises urged to act now on post-quantum security
Apex champions proactive firewall upgrades for MSPs
Interviews
Interviews and video coverage from the networkRecent Encryption News
Indian & global startups race to defend data from quantum threats
Indian and global startups are pioneering quantum-safe encryption to secure data against emerging threats from powerful quantum computers.

Finkeda enhances fintech security with blockchain tech
Finkeda is combating fintech cybersecurity threats by integrating advanced blockchain and robust protocols to safeguard financial data against rising breaches.

Karnataka Bank improves communication with TrueConf platform
Karnataka Bank has launched the TrueConf platform across 900 branches, boosting productivity and ensuring secure digital communication for 15,000 employees.

RansomEXX ransomware disrupts India's banking services
A cyberattack by RansomEXX has disrupted services at around 300 Indian banks, affecting ATMs and UPI transactions. CloudSEK investigates the breach.

KnowBe4 partners Secure Code Warrior on AI training
Organisations using AI in software development will get training on secure coding and governance as vulnerabilities and data risks mount.

BlackFog says only one in nine ransomware attacks go public
Undisclosed attacks outnumbered public cases by nine to one, with healthcare and government still bearing the brunt of the ransomware threat.

Red Hat adds post-quantum security to Linux platform
Quantum-resistant encryption and AI-driven automation are coming to Red Hat Enterprise Linux, as customers face tighter security and less manual upkeep.

apexanalytix launches Qubiton for AI-powered supplier checks
Businesses can now run supplier, tax and sanctions checks through AI tools, as apexanalytix opens access to more than 280 million records.
Celebrity stalkerware leak exposes private messages online
A misconfigured database left 86,859 images and private chats from a prominent European celebrity’s device open to anyone online.

Rippling launches SOC 2 compliance tool for IT teams
Compliance checks can now draw on existing workforce data, cutting months of manual SOC 2 prep for IT teams already using Rippling.

Entrust & IBM Consulting team up on quantum-safe security
Large firms face mounting pressure to unify cryptography oversight as quantum risk and regulatory scrutiny make legacy encryption harder to defend.

Bitcoin rebounds as institutional demand & tokenisation grow
Spot Bitcoin ETF inflows hit their strongest level since October 2025 as large banks and asset managers expanded digital asset plans.

Dell expands cyber resilience with quantum-ready PCs
Security teams face new pressure to protect AI data and backups, as Dell adds quantum-ready safeguards and faster recovery tools.

Bitdefender warns journalists on phishing & source safety
Reporters face rising risks from phishing, spyware and device compromise as Bitdefender urges tighter source protection and account security.

ClickHouse deepens Google Cloud tie-up with four updates
Enterprises could query lakehouse data without moving it, as the database firm adds managed deployment, Arm processors and AI tools on Google Cloud.

Thales launches Imperva for Google Cloud in controlled availability
Customers can keep existing workflows as web application and API protection moves inside Google Cloud, reducing latency and operational overhead.

Ant International upgrades Alipay+ with privacy tech
Encrypted processing will let partners handle cross-border payments while keeping customer data private, as Alipay+ is used by 1.8 billion accounts.

Google Cloud unveils agentic enterprise infrastructure tools
The rollout aims to help businesses run autonomous AI agents more securely, while easing data, networking and sovereignty constraints.

Dell launches PowerMaxOS 10.4 with faster, safer storage
Enterprise users can now cut response times by up to 25% while adding ransomware detection, single sign-on and migration tools.
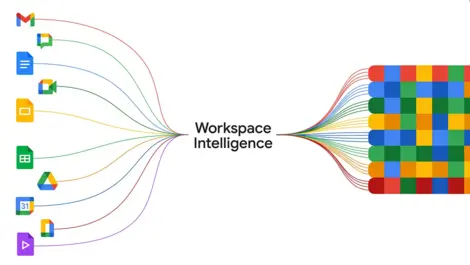
Google launches Workspace Intelligence for AI across apps
The rollout aims to cut time lost switching between apps by letting Gemini draw on emails, files and chats in one workwide context.

